Emotet Trojan is back with a new Office phishing campaign
2 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
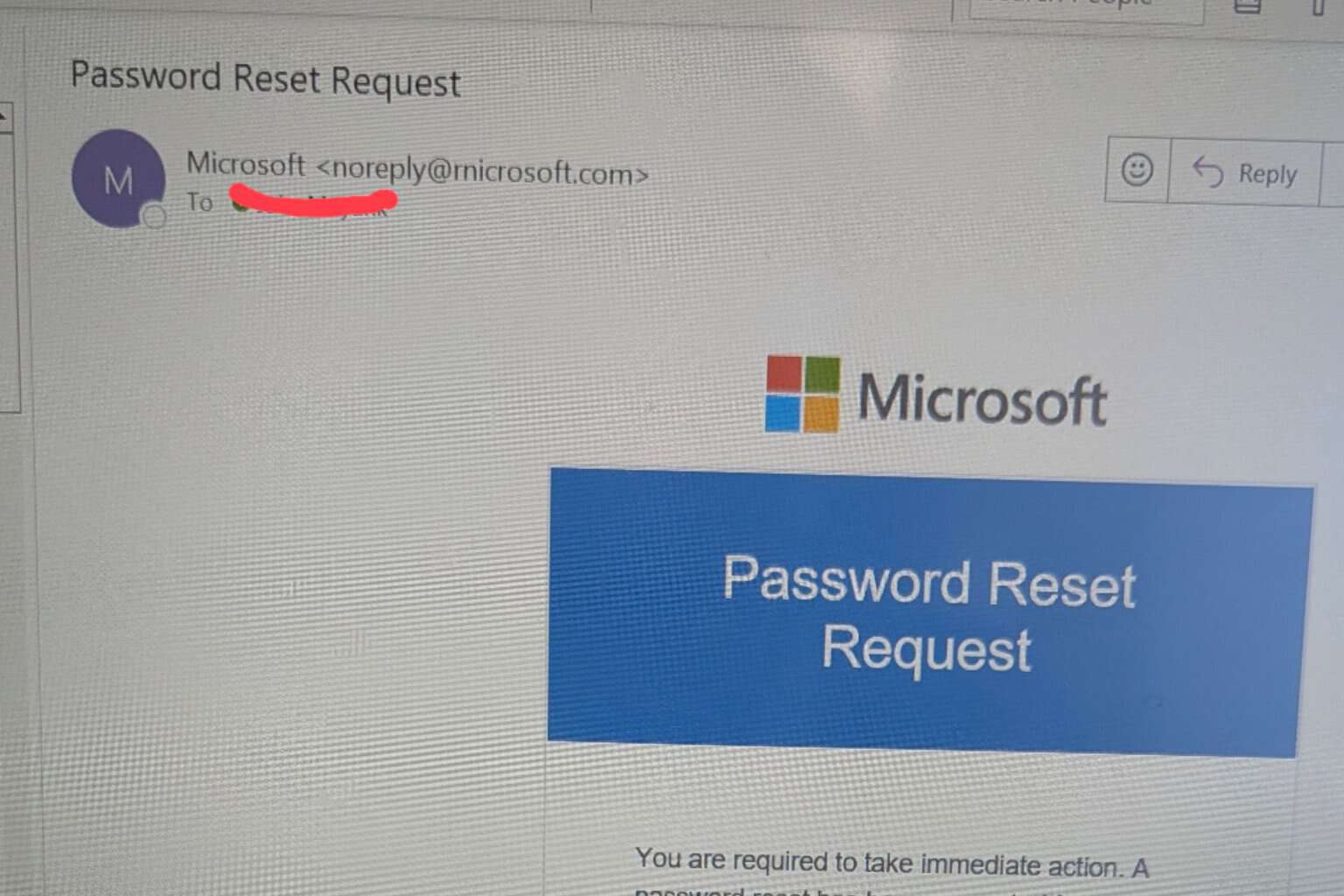
- The Emotet banking Trojan is back with a new Microsoft Office phishing scam.
- If you're targetted, you will receive a malicious email that will contain a URL or an infected Office document.
- There are tough times for security. Read more about it from our Cybersecurity section.
- Are you interested in more news about security? Start from our Security News Hub.

The Emotet banking Trojan returned after a 5 months break with a new Microsoft Office phishing scam.
Emotet goes back a long way since 2014 and has intermittently come back with a taste for your banking credentials and stealing your money.
It’s a serious security issue so it’s time to remind you once again to protect yourself with the best antivirus software and to constantly update them to stay protected.
Emotet Trojan was spotted again after a 5 months break
Emotet was detected again by the specialists from Malwarebytes Labs on July 13th and they followed its trail until July 17th when it started to push malware spam.
Malwarebytes experts say that Emotet is using the same techniques as it employed previously.
If you’re targetted, you will receive a malicious email that will contain a URL or an infected Microsoft Office document.
When you open the document, that will trigger a macro with an error message for you to enable the macro.
After you will enable the macro, WMI will launch PowerShell to retrieve the Emotet binary from one of the remote compromised websites.
Once the package is executed, that will send a confirmation back to one of Emotet’s command and control servers and it will start doing damage.
Of course, that means stealing your banking passwords and trying to draw money from your account.
How can I protect my computer from Emotet?
The most important thing to do to protect your computer from Emotet or any other malware is to restrain from clicking on links or opening documents that you don’t recognize.
As Emotet is not a new threat, we have an excellent guide on how to protect your computer from Emotet trojan.
If you had any problems with Emotet or any other trojan or malware, tell us your story in the Comments section below. Stay safe!
[wl_navigator]





User forum
0 messages