Emotet banking Trojan: How to protect your Windows PC
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

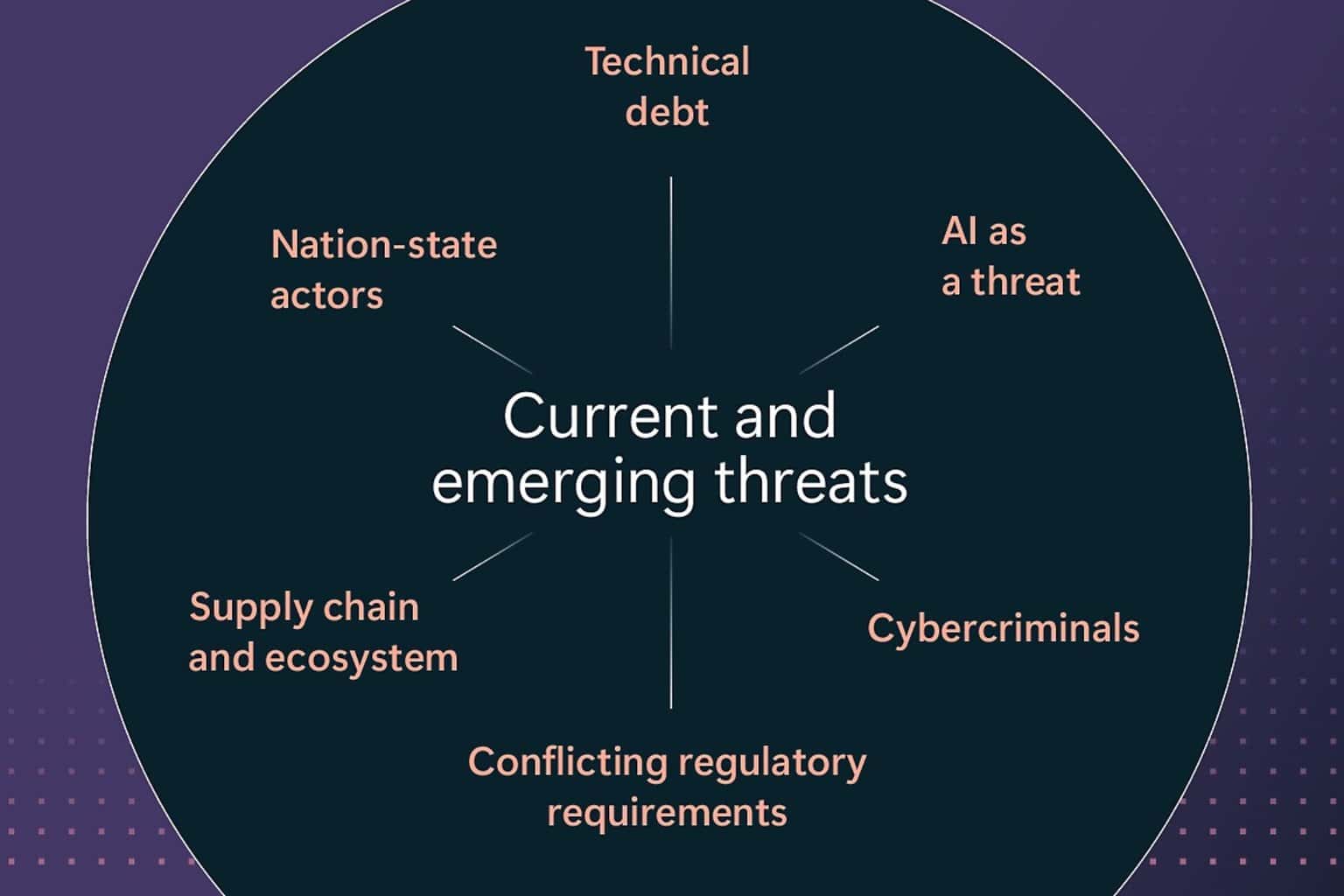
Emotet is a banking Trojan that has been around for some time. Recent reports suggests that the malware became even more vicious and can elude most popular antivirus tools.
Security researchers from Bromium Lab warned that its creators repacked the malware’s code into a unique executable for each and every potential victim. In this manner, it avoids any-and-all signature-based detection.
The good news is that there are still some things that you can do to protect your Windows PC against this virus and avoid infection.
Repacked dropped executables on this scale are unprecedented, and this is why application isolation and control is so important. Protect before you detect is the only secure approach.
Although we have seen this with polymorphic documents, repacked dropped executables on this scale are unprecedented. This is why detect-to-protect security approaches won’t work. […] The scale we see on these samples suggests they may be more than just a few steps ahead.
Follow the steps listed below and you should be able to block the Trojan from getting into your computer.
Block banking Trojan on Windows PCS in 2018
1. Install a reliable antivirus
While free antivirus tools come in handy, they only offer limited features. As a result, they are not powerful enough to protect your device in case of a massive malware attack.
On the other hand, paid antivirus software brings a series of additional features to the table that enhances your computer’s security level.
The good news is that you don’t need to shell out hundreds of dollars to get your hands on a really good antivirus.
You can get one for prices ranging from $30.00 to $50.00, or less than $100.00.
When it comes to good antivirus software, we recommend installing tools such as ESET, Bitdefender, or Panda.
For more information on the best antivirus to use in 2018, check out the articles below:
- Best antivirus software to use for online banking
- Best Antivirus software to use in 2018 for your Windows PC
- 5 best antivirus with tune up to shield your computer
2. Use Virtual Machines
A virtual machine emulates your PC providing the same functionality. One of the advantages of using a virtual machine consists of blocking malware and other threats in a closed environment where they can’t escape from.
In this manner, they can’t actually affect your computer.
So, for example, opening malicious email attachments on a virtual machine allows you to isolate the threat and prevent infection.
For more information on virtual machines, check out the following articles:
- Application Guard lets Microsoft Edge work in virtual machines
3. Avoid visiting fishy websites
Prevention is better than cure. Avoid visiting suspicious websites and don’t download anything from them. Also, keep in mind that free software often come packed with adware and other malware.
Try to download software only from reliable sources or from the developer’s website as much as possible.
4. Don’t open emails or email attachments that you didn’t request
Hackers are resourceful people, and come up with innovative ways to infect your computer. Nevertheless, they often resort to old-fashion methods to install malicious code on your device, including email attachments. Simply ignore these.
5. Beware of public Wi-Fi networks
Connect to public Wi-Fi networks only when absolutely necessary. Since so many people connect to these networks every day, hackers take advantage of that to spread malware.
For more tips on how to stay safe on public Wi-Fi, check out the article below:
6. Install the latest Windows updates
Microsoft regularly rolls out system updates to add new OS features and improvements, and enhance Windows security. The best solution is to set updates on Automatic Mode to make sure that you install them as soon as they’re available.
Keep in mind that prevention is always better than cure. Follow the steps listed above and you should be able to keep banking Trojans at bay.



User forum
0 messages