Researchers sandbox Windows Defender and here are the results
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
The software experts from Trait of Bits, a well-known security R&D company sandboxed Windows Defender to see what could happen.
In case you didn’t know, sandboxing is a tech term that refers to the act of running an app inside a dedicated container. These containers are extremely restricted, and they prevent attacker’s from exploiting OS and app vulnerabilities.
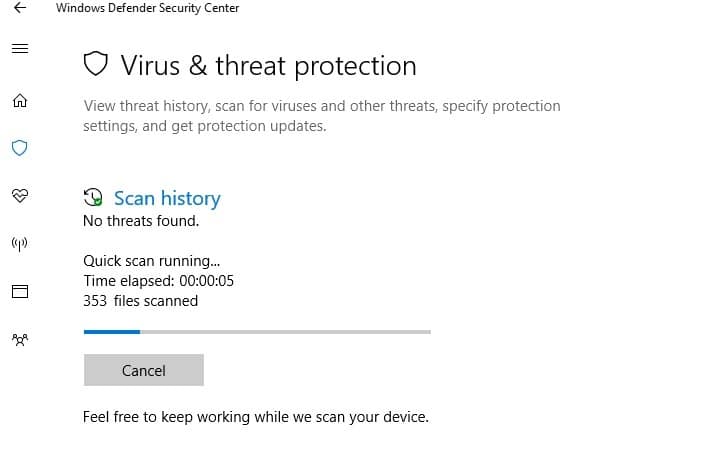
Windows Defender doesn’t run in a sandboxed environment
Windows Defender has been an essential part of the Windows app portfolio for 13 years, but it doesn’t run in a sandboxed environment by default. Modern apps such as Chrome or the Java virtual machine use app containers to protect their users against cyber attacks.
Severe bugs flooded Windows Defender
During the past months, Google engineers (part of the Project Zero security team) have proven the high vulnerability of Windows Defender by exposing multiple bugs. Hackers could exploit these security issues to to take full control over vulnerable machines.
Microsoft engineers did sandbox a few Windows apps such as Device Guard to keep Windows systems safe. Compared to previous operating systems, Windows 10 is extremely well protected.
The AppJailLauncher sandboxing framework
The ToB team developed a framework coded in Rust that runs Windows apps inside their own sandboxes. They also open-sourced the framework on GitHub. You will find it there as AppJailLauncher.
The AppJailLauncher will allow you to wrap the I/O of an app behind a TCP server allowing the sandboxed app to run on an entirely different machine for stronger security.
The researchers have also open-sourced the sandboxed version of Windows Defender on GitHub through the project called Flying Sandbox Monster.
The experts from Trail of Bits have also pointed out the reason for which Microsoft didn’t sandbox Windows Defender – it’s all about the app’s potential performance dip. However, team proved that Windows Defender can be sandboxed without affecting performance-related metrics.
RELATED STORIES TO CHECK OUT: