Zepto ransomware is back, Windows Defender can't block it
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Zepto ransomware is a very sneaky program that has been bugging Windows users for quite a while now. First detected in July, it appears that this malware has become more active since the beginning of September, with more and more users reporting attacks.
Zepto usually enters your computer with the help of other virus programs. Attackers rarely use common tricks, such as specially crafted emails or links to sneak this virus into your computer.
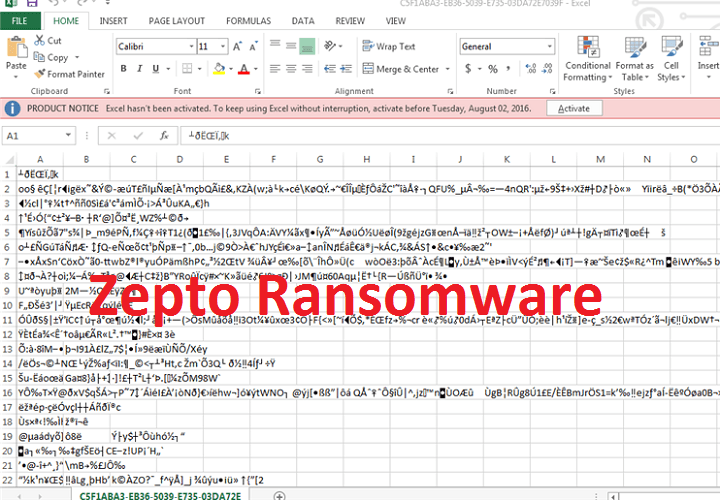
Zepto uses the typical ransomware modus operandi: once it infects your computer, it immediately encrypts your files and directs you to a link where you can pay the ransom. You can easily recognize Zepto’s attacks by the .zepto extension it adds to your files.
Windows Defender fails to block Zepto ransomware
My computer has recently been infected by malware converting all my Word and Excel files to a .zepto extension and a long number name. I have downloaded Windows Defender Offline and tried to run it from a USB drive, but it appears that the malware is preventing it from running.
Unfortunately, the files ecnrypted by Zepto cannot be decrypted. Paying the ransom could help you regain access to your files, but this only helps the attackers to reach their goal. One solution to avoid such issues is to use a cloud file storage service such as OneDrive or Dropbox. In case you become the victim of a ransomware attack, you can always restore the files after you clean the computer.
Speaking of malware, there is another vicious ransomware lurking in the dark. Cerber3, the third generation Cerber ransomware can also go undetected by Windows Defender, but at least uses more “suspicious” entry gates, such as emails and specially crafted links.
Taking into account the frequency of malware attacks, using an anti-ransomware program could save you the headache of restoring your files following ransomware attacks. Install one of these anti-malware programs to add an extra layer of protection to your system, and avoid installing obscure software, following suspicious links or opening suspicious emails.
RELATED STORIES YOU NEED TO CHECK OUT: