12 Best Anti-Data Mining Software to Keep Hackers at Bay
Keep hackers away from your PC and try these anti-malware tools
Key notes
- Data mining protection software is another term to describe anti-malware tools.
- So if you want to be better informed on how to prevent data mining, you should use an antivirus, but not exclusively.
- Stand-alone firewalls, password managers, or VPNs are also among data mining prevention techniques.
- Sometimes you can have more of these tools incorporated in the same software.
Data mining is a process that involves discerning patterns to acquire information concerning a data set. For instance, data mining involves the prediction of a computer user’s Internet activity to obtain behavioral characteristics.
In addition, some hackers, spammers, and even scammers utilize data mining tools for negative purposes. There are several reports relating to online identity theft, impersonation, and several online fraud cases.
Meanwhile, hackers use several data mining tools and techniques to steal users’ personal information, discover their identities, and exploit users’ data. Some of the tools and techniques are listed below:
- Keyloggers – software that tracks the key sequence and strokes on your keyboard. Fortunately, you can install anti-keylogger software to block this type of tool.
- Malware – short for malicious software which refers to various forms of hostile or intrusive software.
- Phishing – the attempt to acquire sensitive data by disguising it as a valid entity on the web.
- SMShing – this technique involves using mobile phone text messages, to lure users into downloading content online, or visiting a phishing website.
- Virus – malicious codes that delete or corrupt files, and also interfere with normal computer operations
- Session hijacking – the unauthorized usage of identification credentials within a web browser to hijack a valid web session. Also known as cookie theft.
The Windows Report team has compiled the best tools for you to protect your computer against data mining and its minions. These tools give you maximum protection in securing your personal information and identity.
What is the best tool to block data mining attempts?
ESET HOME Security Essential – Lightweight software
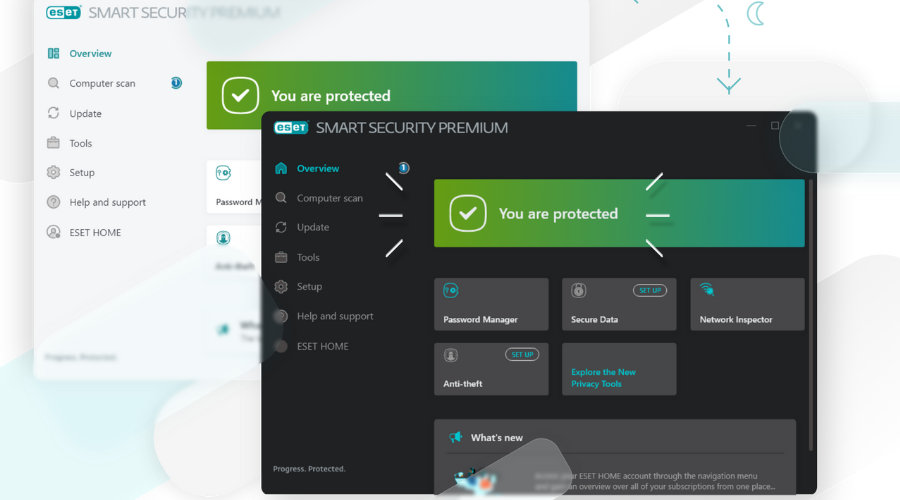
ESET is a well-known brand in the online security environment. Their antivirus solutions protect against any type of malware, including viruses, ransomware, worms, and spyware.
Once installed, the solution is lightweight, unintrusive, and efficient. ESET secures your online operations, monitors your connected devices, and continuously works in the background to ensure seamless protection.
The tool comes in three variants: Essential, Premium, and Ultimate. We’re recommending HOME Security Essential as being the best option when it comes to features offered for this price.

ESET HOME Security Essential
Protect your digital activity against data mining with the powerful ESET technology that has protected millions so far.Bitdefender Total Security – Social network protection
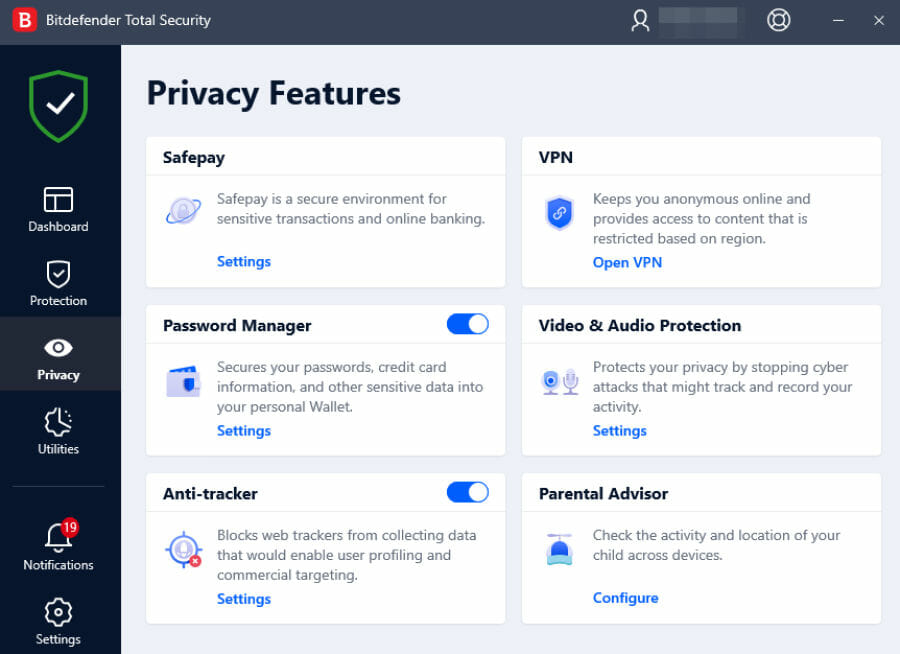
Bitdefender Total Security, as its name implies, defends every bit of information on your PC. If you want protection against any tools utilized by data hijackers, then you should consider this software which has one of the largest security infrastructures worldwide.
This anti-data mining software offers 3P i.e. protection, performance, and privacy. It also ranks highly in each AV Lab test performed independently.
Here’s what to expect from Bitdefender:
- It comes with protection tools such as antiphishing, antivirus, anti-fraud, and anti-theft
- It also has webcam protection to prevent snooping
- Multiple-layer ransomware protection
- It comes with Bitdefender VPN for anonymous online identity
- Social network protection
- Password manager
In addition, other tools include file shredder, game, movie, and work modes, secure browsing, battery mode, rescue mode, parental control, and many more.
It is compatible with all recent versions of Windows, starting with Windows 7 SP1, and offers top performance, especially on Microsoft Windows 10.

Bitdefender Total Security
Outstanding security app that offers complete protection against all e-threats.Avira Free Security – Multiple threat protection
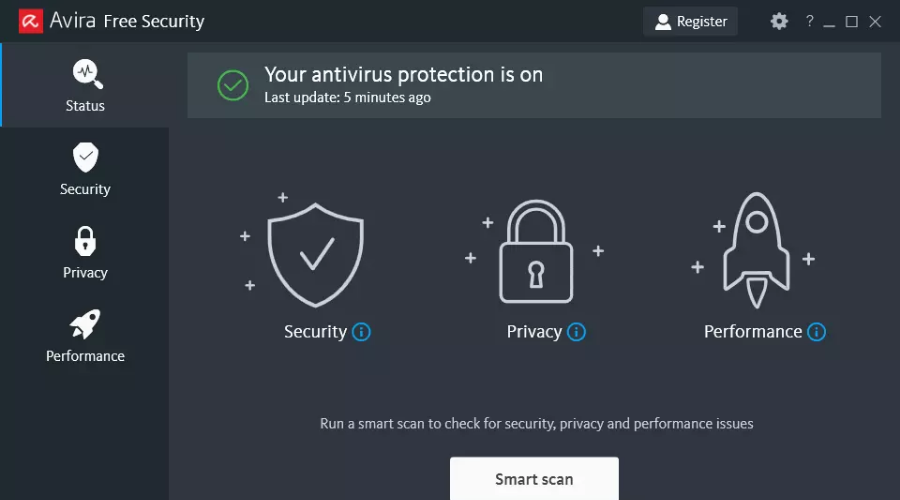
This software offers basic protection against the most common cyber-attacks: spyware, malware, ransomware, and phishing. The real-time protection feature is active at all times to ensure that your devices are secure.
Indeed, the tool is free, but, as you can imagine, it comes with just a few features. If you want to further increase protection for other areas such as getting strong passwords or tune-up tools, you can always upgrade to a more advanced solution.
For instance, with Avira Prime-only you get to optimize your PC or use the built-in VPN without restrictions.

Avira Free Security
Want only some basic protection for your device? Avira offers just that, packed with free, lightweight, efficient software.Malwarebytes Premium – Vulnerability prevention
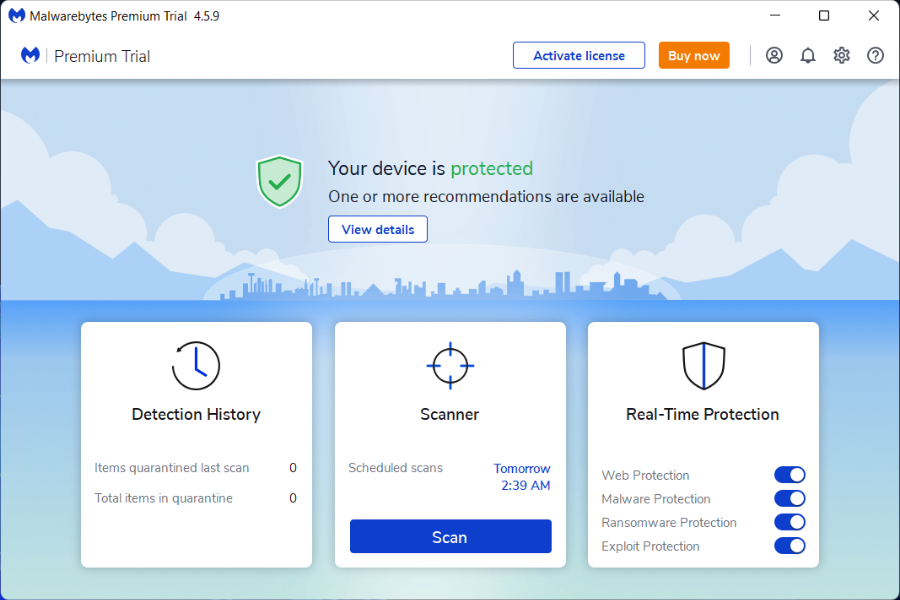
Just as its name implies, Malwarebytes protects your computers from malware. Effective as anti-data mining software, your data is shielded with this multipurpose cybersecurity tool.
Here are some features of Malwarebytes:
- Real-time protection against viruses, malware, adware, and spyware
- Excellent antiphishing protection against malicious websites
- Anti-exploit tool to prevent system vulnerability exploits attacks.
- Anti-ransomware protection
- Anti-rootkit tool for removing rootkits and repairing damaged files
Also, this anti-data mining software is compatible with Windows XP up to Windows 10. However, the anti-ransomware protection is only available on Windows 7, Windows 8.1, and Windows 10.

Malwarebytes Premium
Prevent digital threats from compromising your device with the Malwarebytes Premium software.SpyShelter – Optimized performance
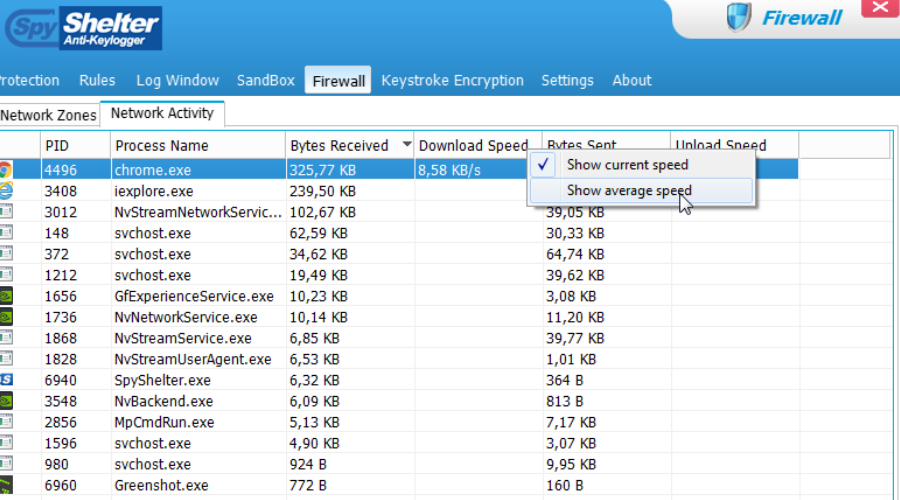
Ranked as the world’s number one anti-keylogger software, this software also functions effectively as anti-data mining software. With a nice GUI, even beginners can find it easy to use.
This tool consistently monitors all the vulnerable areas on your Windows PC; this ensures that your personal data is protected from wicked data mining software.
Also, this Windows OS-friendly software ensures you don’t lose your private data such as credit card data, chat messages, and passwords.
Here’s what you should expect from SpyShelter Free:
- Strong behavior-based real-time protection against stealing your private data like passwords, chat messages, or credit card data.
- Efficient detection and neutralization of advanced zero-day malware
- Encryption of keys of all applications on kernel level.
- Microphone and webcam protection
- Low system resources used for increased performance
Also, this anti-data mining software has other features such as:
- Alerts and Rules
- Clipboard Protection
- Screen capture Protection
- Sound logger Protection
- Restricted Applications
- Two-way Firewall
So, you can combine this software with your antivirus program; this is because SpyShelter is compatible with most antivirus programs and other security programs on your system. Also, it is compatible with Windows OS (from Windows XP to Windows 10).

SpyShelter
Strong protection with high detection scores that block all types of malicious threats.Avast Free Antivirus – Latest e-threat detection
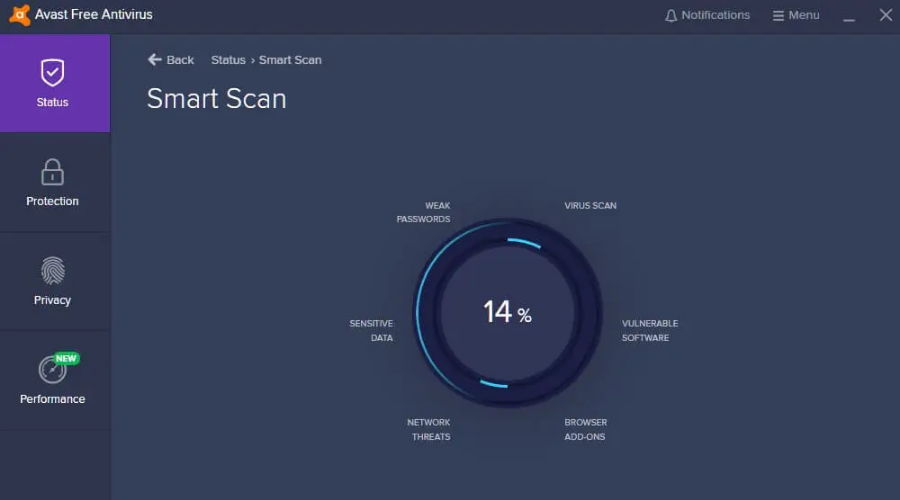
Don’t be put away by the fact that this product is free. It’s nevertheless efficient when it comes to detecting the latest cyber threats as it uses the same technology as paid products.
Additionally, it offers Wi-Fi network protection and document encryption functionalities, which regular free software doesn’t include.
Of course, you can have more options such as webcam security, or an extra layer of protection while doing online shopping, but with premium products.

Avast Free Antivirus
The most efficient free antivirus that offers great protection features for your device.Dr.Web KATANA – Web link checker
Another best anti-data mining tool on the market, Dr.Web KATANA shields vulnerabilities that expose your computer to data mining. Dr. Web was founded by Igor Daniloff in 1992, in Russia.
This software is efficient in neutralizing remote-controlled malware used for data mining. Also, Dr.Web is linked to a cloud facility that acquires information about data mining espionage and blocks it promptly.
Here’s what to expect from Dr.Web KATANA:
- Real-time protection against viruses and malware
- Efficient detection and neutralization of all types of threats including unauthorized network access
- Comprehensive protection against data leaks
- Web browser protection against cookie hijackings
- Web CureIt for curing Windows PCs and servers
- Web Live Disk for PC recovery
- Web Link Checker for browser plugins
Additional security tools against data mining:
We also made a quick list of supplementary security programs to defend your device against malicious software and malware.
Maintain your data and personal information secure by benefiting from all these advanced technology features that proactively block all e-threats.
Browser

A secure web browser is a category of web browsers that provides data confidentiality online. This means that all your browsing information is spoofed; hence, your browsing data cannot be accessed for data mining.
However, this is also possible on normal web browsers, where you just have to press the CTRL-Shift-Delete keys to clear your cache. But, a more secure web browser is advisable in case you forget the keys.
Safeness, rapidity, and security are certainly some of the many reasons people choose to use private browsers for their PCs.
VPN

VPN stands for virtual private network which is a private network that extends across public networks most especially the internet. In addition, they enable secure access, anonymous identity, and virtual privacy on the internet; hence, your personal data and location are spoofed making it ideal to escape data mining agents.
Also, VPN protects your online privacy and gives you better internet connectivity, and access to limited resources.
1. PIA
Private Internet Access (PIA) keeps your personal data safe from ISPs, and the government. In addition, you get features like DNS and IP leak protection, a strict no-logs policy alongside 256-bit AES encryption for maximum security.
If you want access to thousands of servers worldwide, unlimited bandwidth, and traffic, at the highest possible speed; CyberGhost is the ideal tool for this purpose.
Password Manager
A password manager is a software application that stores and manages your passwords. This provides enhanced security for recollecting passwords for various online accounts instead of saving the passwords on your web browser.
Check our top password managers for Windows 10.
? Tips for preventing data mining:
- Create a guest account for “guests” to use your device to keep your sensitive data safe.
- Avoid using public Internet connections such as Wi-Fi hotspots or public computers to enter your online account credentials.
- Beware of clicking download links you are not sure of when checking your emails.
- Keep your antivirus or security program constantly updated.
- Use secure devices for internet banking.
- Shun using the remember password option or auto-complete feature on your web browser.
- Ensure your browser is completely closed after you are done surfing the web.
- Update your Windows OS, web browsers, drivers, and other software applications regularly. You may consider using Outbyte Driver Updater as well.
Conclusively, we do hope that you find our list of best anti-data mining software useful in preventing data leaks and cyber espionage on your system.
Have you used any of the tools we mentioned above? Feel free to share your experience with us by commenting below.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more







User forum
0 messages